Implementation of Block-Level Double Encryption Based on Machine Learning Techniques for Attack Detection and Prevention

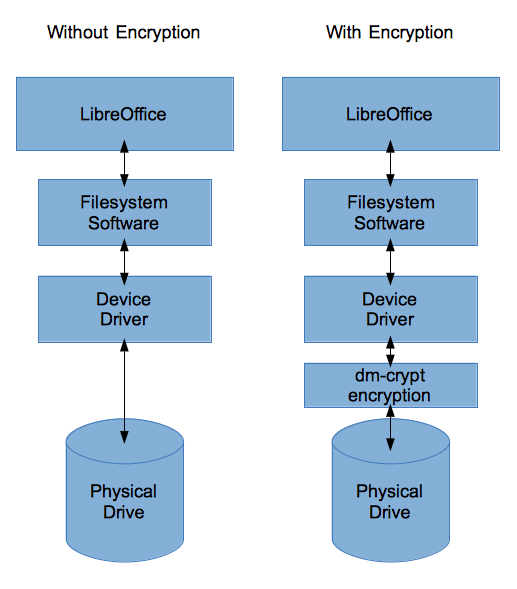
Block level representation of the proposed system. The upper flow shows... | Download Scientific Diagram

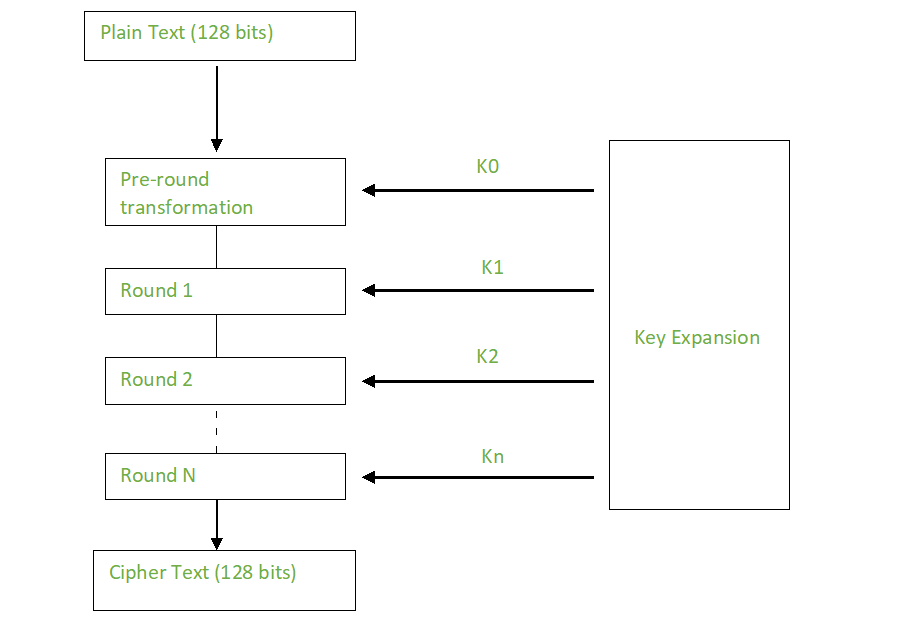
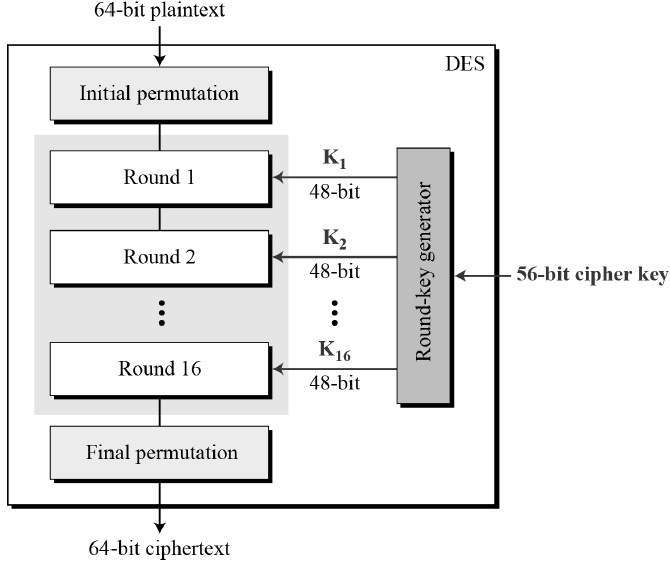
A Comparison of Cryptographic Algorithms: DES, 3DES, AES, RSA and Blowfish for Guessing Attacks Prevention
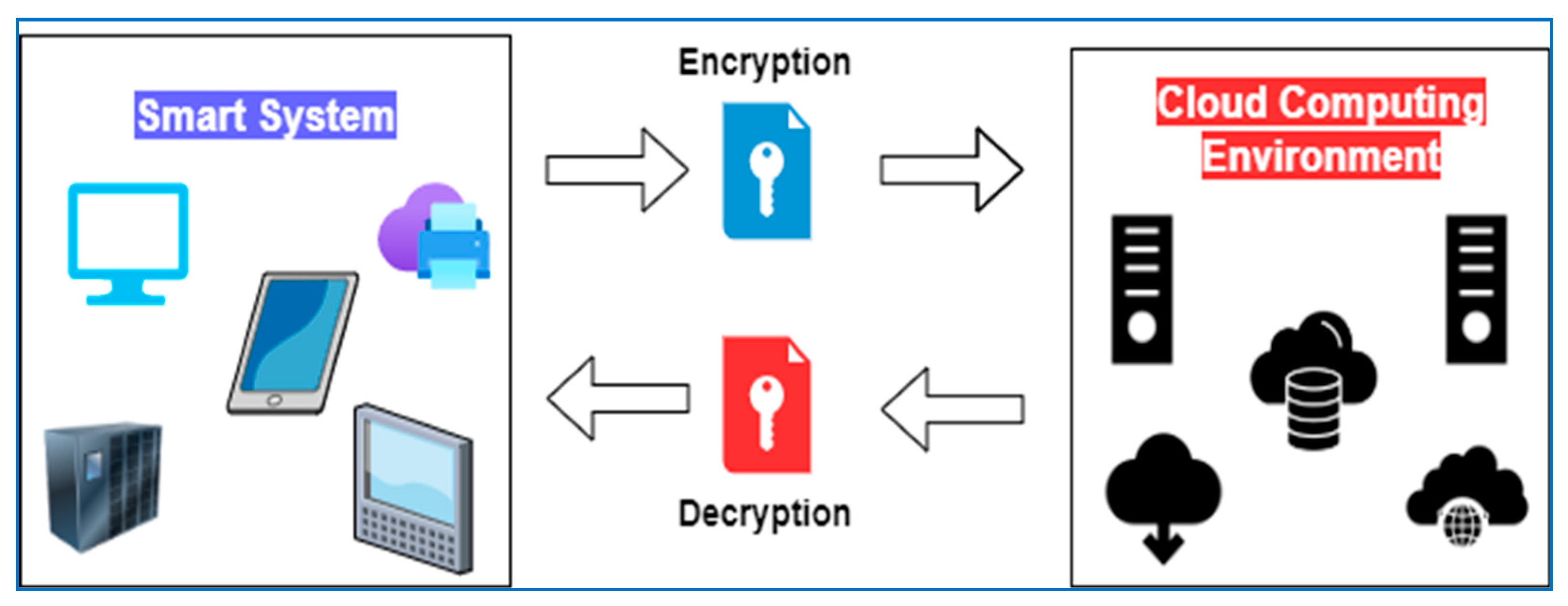
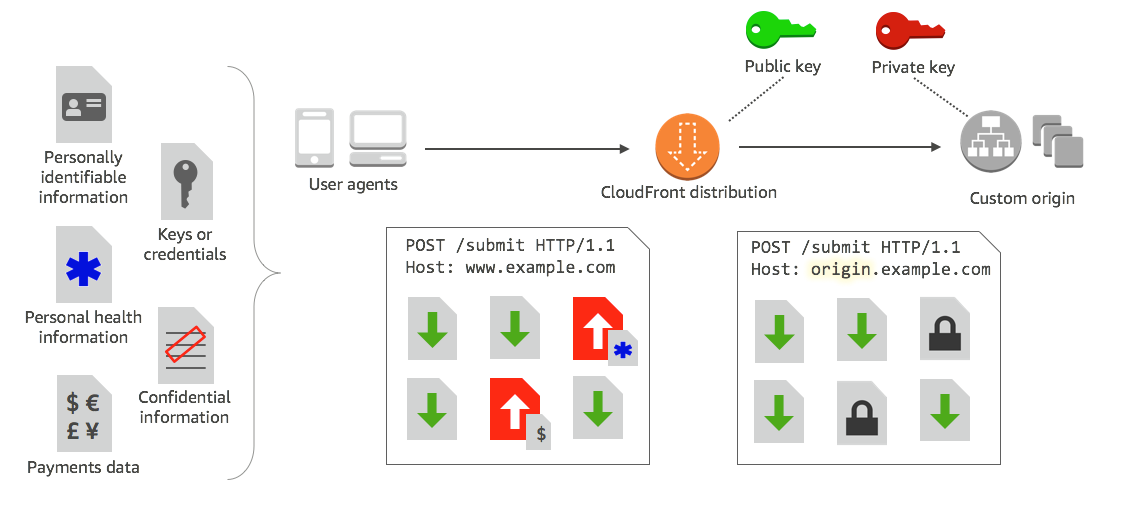
Symmetry | Free Full-Text | Encryption Techniques for Smart Systems Data Security Offloaded to the Cloud
![PDF] A New High Capacity Separable Reversible Data Hiding in Encrypted Images Based on Block Selection and Block-Level Encryption | Semantic Scholar PDF] A New High Capacity Separable Reversible Data Hiding in Encrypted Images Based on Block Selection and Block-Level Encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9d272b8844671af412035ad31d594728630ec326/3-Figure2-1.png)



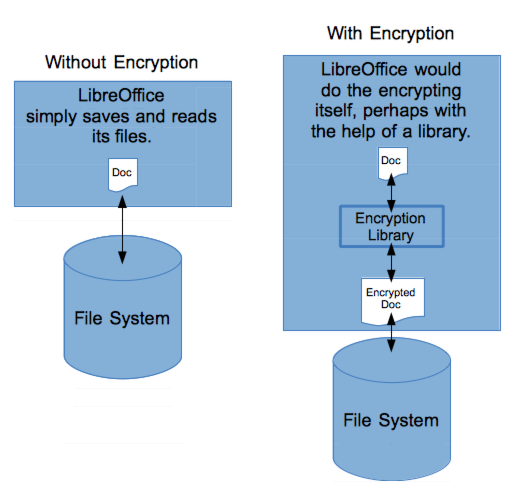
/filters:no_upscale()/articles/ale-software-architects/en/resources/17image009-1608134749187.png)



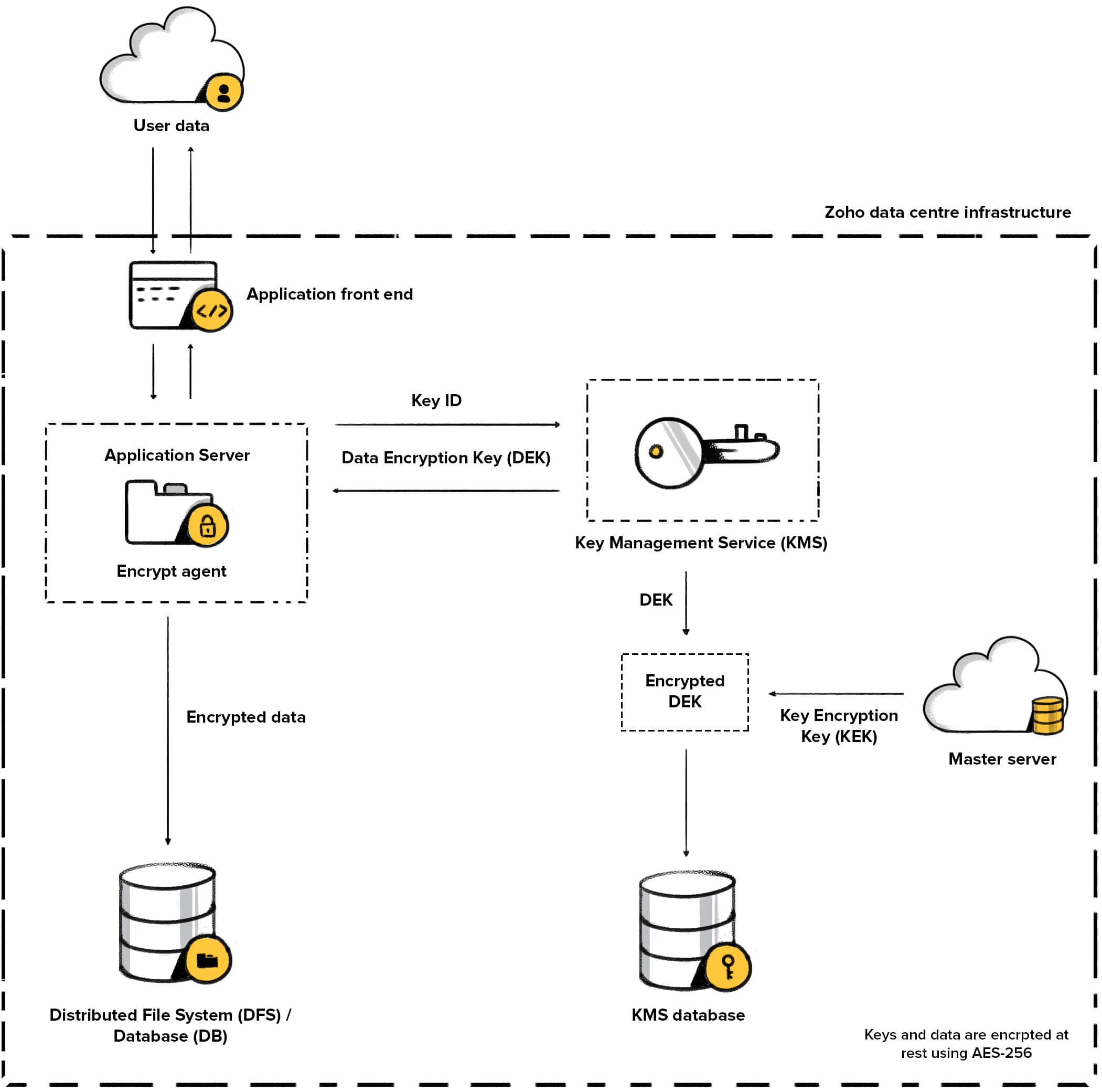


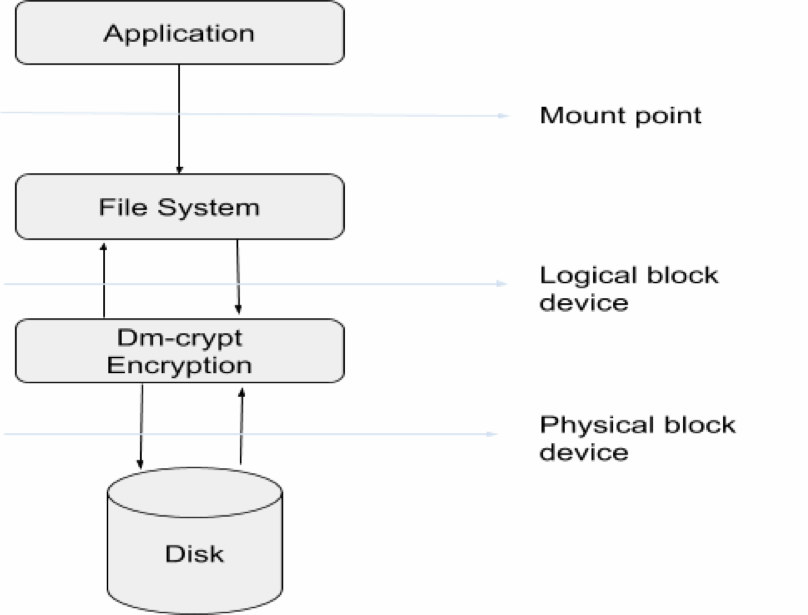

![PDF] Block-level De-duplication with Encrypted Data | Semantic Scholar PDF] Block-level De-duplication with Encrypted Data | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d2b0011068d3140cff0c7e796f0bac6dea3d2f15/3-Figure1-1.png)